Disclaimer: This blog offers general information and should not be considered legal advice. Consult your own legal counsel for specific advice.
On 14 December 2022, the European Commission published “Directive (EU) 2022/2555 on measures for a high common level of cybersecurity across the Union,” otherwise known as the NIS2 Directive. Due to its broad reach and significant impact on the EU and non-EU entities, it is important to understand which entities are subject to it and the obligations imposed. This blog aims to demystify NIS2 by summarizing over 80 pages of legislative text into language that everyone can understand.
When will NIS2 measures become effective?
18 October 2024.
Which entities are subject to NIS2?
NIS2 broadly covers two types of entities: “essential entities” and “important entities.”
“Essential entities” include (1) the 11 types of entities listed below that meet the size threshold. An entity meets the size threshold if it employs over 250 persons, has more than EUR 50 million annual turnover and/or EUR 43 million in total annual balance sheet, and (2) all qualified trust service providers, top-level domain name registries, DNS service providers, critical entities and public administration entities regardless of size.
| Essential Entities:
Energy (electricity, district heating and cooling, oil, gas and hydrogen); transport (air, rail, water and road); banking; financial market infrastructures; health including manufacture of pharmaceutical products including vaccines; drinking water; waste water; digital infrastructure (internet exchange points; DNS service providers; TLD name registries; cloud computing service providers; data centre service providers; content delivery networks; trust service providers; providers of public electronic communications networks and publicly available electronic communications services); ICT service management (managed service providers and managed security service providers), public administration and space. |
“Important entities” include entities listed above that do not meet the size threshold, or any of the following types of entities:
| Important Entities:
Postal and courier services; waste management; chemicals; food; manufacturing of medical devices, computers and electronics, machinery and equipment, motor vehicles, trailers and semi-trailers and other transport equipment; digital providers (online marketplaces, online search engines, and social networking service platforms) and research organisations. |
Each Member State has the discretion to designate an entity as an “essential entity” or “important entity” beyond what is listed above.
The final lists of essential & important entities, together with entities providing domain name registration services, will be established by the Member States by 17 April 2025.
To avoid regulation overlap, NIS2 obligations do not apply to entities subject to requirements under another EU sector-specific rule that are “at least equivalent in effect.” For example, financial institutions subject to Digital Operational Resilience Act (DORA) do not need to comply with NIS2’s incident reporting or measure adoption requirements.
Will non-EU entities be subject to NIS2?
A non-EU essential or important entity will be subject to NIS2 if it provides services in the EU.
Even if an entity is not subject to NIS2, it will likely be affected due to “supply chain flow-down.” If an entity has a customer (or a customer of a customer) that is an “essential entity” or “important entity”, such customer would require the entity to comply with the applicable NIS2 rules to ensure its own compliance in the event of a cyber incident or regulatory audit, for example.
What are NIS2’s key requirements?
Minimum Measures
Rather than leaving it to the entities to adopt best practices, NIS2 requires all entities to implement a minimum list of 10 basic security elements. The elements include incident handling, supply chain security, vulnerability handling and disclosure, the use of cryptography and where appropriate, encryption, business continuity, basic cyber hygiene such as MFA and authentication, and training.
Incident Reporting & Vulnerability Disclosure
NIS2 lays out a multi-staged incident reporting framework with a fast timeline. Affected entities must report any “significant incident” to their CSIRT (computer security incident response team) or competent authority as follows:
- early warning within 24 hours;
- incident notification within 72 hours;
- intermediate report upon request; and
- final report within one month.
Where appropriate, notices to such entities’ customers and/or the public may be required.
Individuals and entities are also required to report newly discovered vulnerabilities to CSIRT. The EU Agency for Cybersecurity (ENISA) is to develop and maintain an EU vulnerability database.
Registration
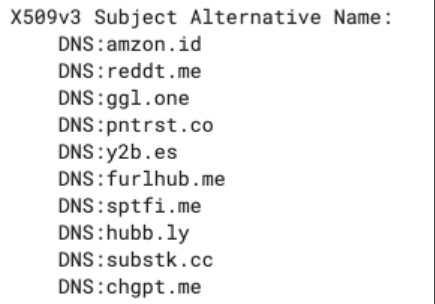
Certain digital infrastructure and digital providers will be required to submit information to competent authorities to enable ENISA to maintain a registry of such entities. These entities include providers of DNS service, TLD name registration, cloud computing, data centre, content delivery networks, managed services, managed security services, online marketplaces, online search engines and social networking services platforms.
How will the EU enforce NIS2?
To address inconsistent enforcement across the EU, NIS2 provides a minimum list of supervisory means, including regular and targeted audits, on-site and off-site checks, request of information, and access to documents or evidence.
What sanctions will be imposed for violations?
NIS2 requires each Member State to establish a minimum list of administrative sanctions for violations. These sanctions include binding instructions, order to implement the recommendations of a security audit, order to bring security measures in line with NIS requirements, and administrative fines.
NIS2 mandates a maximum administrative fine of at least the greater of EUR 10 million or 2% of global annual revenue for essential entities, and EUR 7 million or 1,4% of global annual revenue for important entities.
Penalties for non-compliance include not only sanctions for the entity, but also civil and criminal liabilities against management individuals.
What are the next steps?
To stay ahead of the curve on NIS2 compliance, entities should consider the following next steps:
- Monitor implementation of NIS2 regulations by the applicable Member State, and other applicable laws such as GDPR, SEC regulations, DORA, etc.
- Document InfoSec policies and practices to include the 10 basic elements
- Know where your data and assets are
- Focus on supply chain security
- Practice cybersecurity hygiene
- Elevate cybersecurity discussions to the Board of Directors and the C-Suite
- Budget for cybersecurity spend increase
- Evaluate government certification requirements
NIS2 Directive Summary
| TOPIC | DETAILS | ARTICLE(S) & ANNEXES |
|---|---|---|
| General Provisions; Final Provisions; Jurisdiction & Registration | Ch. I (Art. 1-6); Ch. IX; Ch. V | |
| General Information |
|
Art. 1;
Art. 6 |
| Scope | Entities subject to NIS2, namely:
|
Art. 2 para.1-5;
Art. 3 |
Essential entities include:
Important entities include entities listed in Annex I and II that are not essential entities. |
Annexes I & II; Art. 2 of Annex to Recommendation 2003/361/EC | |
| The final lists of essential & important entities, together with entities providing domain name registration services, shall be established by Member States by 17 April 2025. | Art. 3 para. 3 | |
Types of entities excluded from NIS2, including:
|
Art. 2 para.6-11; Art. 4 | |
| Effective Date | Member States shall:
|
Art. 41 |
| Entity Reporting Obligations | Essential & important entities are required to report at least the following information using templates to be provided by the EC:
|
Art. 3 para.4; Art. 27 |
| Registration of Digital Infrastructure and Digital Providers | ENISA shall create and maintain a registry of the following types of entities (collectively, “Digital Infrastructure and Digital Providers”):
|
Art. 27 |
| Domain Name Registration Database | Member States shall create a database of domain name registration data using information provided by TLD name registries and entities. | Art. 28 |
| Jurisdiction | NIS2 applies to:
|
Art. 26 |
| Member States Coordinated Cybersecurity Frameworks; Information Sharing | Ch. II (Art. 7-13); Ch. VI | |
| Cybersecurity Strategy & Policies | Each Member State shall adopt a national cybersecurity strategy, that includes policies on:
|
Art. 7 |
| Competent Authority/ CSIRT | Each Member State shall designate one or more:
|
Art. 9-11 |
| Single Point of Contact | Each Member State shall designate a single point of contact that liaison with other Member States. | Art. 8 |
| Cooperation at EU and International Level | Ch. III (Art. 14-19) | |
| Cooperation Group; CSIRTs Network; EU-CyCLONe |
The following are established at the EU level:
|
Art. 14-17 |
| EU Vulnerability Database | Member States shall ensure individuals and entities report vulnerability to CSIRT.
ENISA shall develop and maintain an EU vulnerability database. |
Art. 12 |
| ENISA Report | ENISA shall issue a biennial report to the EC on the state of security. | Art. 18 |
| Peer Review | Each Member State will be subject to peer review by cybersecurity experts designated by other two Member States. | Art. 19 |
| Cybersecurity Risk-Management Measures and Reporting Obligations by Essential & Important Entities | Ch. IV (Art. 20- | |
| Risk
Management Measures (10 Elements) |
Member States shall approve cyber risk-management measures taken by essential & Important entities and oversee their implementation by following EU and international standards. | Art. 20-21, Art. 25 |
Cyber risk-management measures shall include at least 10 elements:
Implementing acts shall be adopted on the technical and the methodological requirements of the measures for Digital Infrastructure and Digital Providers by 17 October 2024. |
Art. 21-22 | |
| Reporting of “significant incident” within 24 hours | Essential & important entities shall notify any “significant incident”:
|
Art. 23 |
“Significant incident” is an incident that:
|
Art. 23 para.3 | |
| Subsequently implementing acts will be adopted by 17 October to clarify “significant incident” for the Digital Infrastructure Providers and Digital Providers listed above. | Art. 23 para.11 | |
Incident reporting shall be staged as follows:
|
Art. 23 para.4 | |
CSIRT or competent authority shall:
|
Art. 23 para.5-8 | |
| Each Member State’s single point of contact shall submit a summary report of aggregated incidents to the EC every three months. | Art. 23 para.9 | |
| EU Cybersecurity Certification | Member States may require essential & important entities to use products certified pursuant to Art. 49 of Regulation (EU) 2019/881. | Art. 24 |
| Supervision and Enforcement | Ch. VII | |
| Types of Regulatory Oversight | Competent authorities have power to conduct risk-assessed supervision, including:
|
Art. 32 & 33 |
| Penalties against Entities and Individual Management | Competent authorities have power to:
Penalties shall be effective, proportionate and dissuasive. |
Art. 32 & 33 |
| Administrative Fines | For essential entities, the maximum fines shall be at least the higher of:
For important entities, the maximum fines shall be at least the higher of:
|
Art. 34 |