One year after Google .zip TLD (Top Level Domains)’s launch, we take a retrospective look at its impact on DNS security. The introduction of domain extensions mimicking common file extensions was met with both excitement and concern. While it opened new avenues for legitimate use, it also posed significant security challenges, particularly in the realms of phishing campaigns and malware distribution.
Research Overview
EfficientIP has been closely monitoring the Google domains since its inception. Our research involved analyzing approximately 17,000 .Google .zip TLD cybersecurity over the past year in our customers’ traffic. We tracked Google domain registrations, their active versus inactive states, and the nature of user interactions with these domains, categorizing them as safe, suspicious, or malicious. A deeper analysis was conducted on domains containing installers in their HTML, a strong indicator of malicious activity.
Our methodology included:
- Monitoring domain registrations: we observed a surge in registered domains immediately following the TLD’s launch. These early registrations included a variety of uses, from genuine business applications to deceptive and harmful purposes.
- Tracking domain activity: we monitored which domains were active, which had gone down, and which exhibited suspicious or malicious behavior.
- User interaction analysis: we analyzed actual user attempts to access .zip domains and categorized these domains based on their safety.
- HTML content analysis: we performed a deep dive into the content of these domains, especially those that contained installer files, to identify potential threats. Although most of the HTML content consisted of text, the number of domains hosting applications is very concerning.
Research Results Overview
Our analysis provided several key critical insights and findings:
- Domain Registration Trends: There was an initial spike in .zip domain registrations, primarily driven by curiosity and the potential for innovative uses. However, this surge also attracted threat actors looking to register domains and deceive users by exploiting the familiarity of the .zip files extension.
- Active vs. Inactive Domains: Over the year, we noticed a decline in the proportion of active .zip domains. Many domains that were initially registered became inactive or were taken down due to malicious activity or other reasons. . However, the content on these sites remains a concern, with many containing executable files that could be malicious.
- Suspicious and Malicious Content: The proportion of suspicious websites increased from 11.9% to 18.5% over the year. This rise indicates a growing .zip TLD cybersecurity impact. We discovered that many of these domains contained installer files, a significant indicator of potential malware. This trend highlights the increasing use of .zip domains for distributing malicious software.
- Common Malicious Patterns: Our analysis revealed common patterns among malicious .zip domains. These included the use of well-known software update names, eg. “windows-updater.zip,” “msteams-update.zip”, to trick users into downloading malware. This tactic exploits the familiarity and trust users place in these names to increase the likelihood of successful .zip phishing attacks and malware distribution.
Cybersecurity and DNS Security Challenges introduced by Google .zip TLD
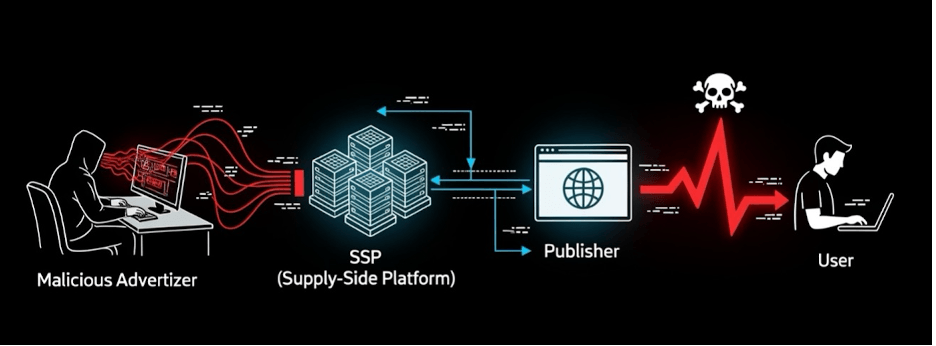
The introduction of Google’s .zip TLD has significantly increased the security risks associated with DNS server due to its resemblance to the common .zip file extension. This resemblance causes confusion for both users and automated systems, leading to several critical vulnerabilities.
Phishing, Domain Spoofing, and Social Engineering
The automatic interpretation of .zip strings as URLs in messaging applications and web browsers presents a substantial risk. For example, text like “update.zip” can be turned into a clickable link. This is particularly problematic in chat applications, where it can trigger DNS or web queries to display a thumbnail of the linked page. In the example below we can see that what appears to be a legitimate link to a file on GitHub might actually direct users to a deceptive domain such as “v15.zip,” exploiting fake characters like confusable fraction slash instead of slash to create a misleading appearance. Such scenarios are prime opportunities for domain spoofing, phishing, and social engineering attacks, where users are tricked into clicking on malicious links, sharing personal information such as credit card data or login credentials, and opening the door for threat actors.

Unintended DNS Queries
Another significant issue is the inadvertent triggering of DNS queries by merely mentioning filenames ending in “.zip” during discussions. This can expose internal information to those controlling the domain’s DNS server. For instance, a filename like “software[.]exe[.]zip” can generate DNS queries to malicious domains, revealing sensitive information. Similarly, searching for non-existent .zip files in Windows Explorer , such as the “prospects.xlsx.zip” below, can lead to unintended online searches, potentially reaching harmful domains.

This problem exemplifies the risk of unintended DNS queries, which can lead to sensitive information leaks or network breaches.
Malware Distribution
The .zip TLD security impact also involves a serious threat of malware distribution. Cybercriminals can exploit the .zip extension to host websites that serve malware disguised as legitimate software. Users might trust a .zip domain for downloading software, thereby increasing the risk of malware infection. Additionally, homograph attacks, where visually similar domain names deceive users into thinking they are accessing a legitimate domain, further exacerbate this risk. Many .zip domains host executable files or archives containing malware. Our 17,000 .zip domains analysis uncovered over 600 instances of Windows Trojans, highlighting the extent of this threat.
Analysis of Domains Activity Over One Year
Our study revealed several key trends in .zip domain activity over the past year:
Domains Registration Trends
There was an initial surge in .zip domain registrations following the TLD’s launch, with a gradual decline in new domain registrations over time. This pattern reflects both the initial excitement and subsequent caution as security issues became apparent.

Active vs. Inactive Domains
The proportion of active .zip domains has slightly decreased since July 2023. Many domains were deactivated or taken down due to their involvement in malicious activities. However, a significant number of these domains remain active and continue to pose security risks.

Suspicious and Malicious Content
The proportion of suspicious websites increased from 11.9% to 14.6% over the year (preventage of suspicious domaines from both active and inactive domains). This rise indicates a growing threat landscape associated with. The analysis of malicious .zip domains in March 2024 reveals that a significant portion remains active, with 60% (1323) from all malicious domains are still operational and posing a threat to users. Notably, out of the malicious domains, 41 contain installer files, which is a strong indication of active malware distribution. The analysis of suspicious .zip domains has similar results – 59% of suspicious domains (1474) were identified as active, with 44 of these domains containing installer files, indicating a considerable threat. When considering both malicious and suspicious .zip domains, it is evident that cybercriminals are exploiting the .zip TLD for harmful activities. This underscores the critical need for enhanced detection mechanisms, rapid response strategies, and user education to safeguard against these threats.

In-Depth Analysis of Google .zip TLD Domains Names
Not surprisingly, many of the analyzed Google .zip TLD domains included extensions mimicking common, widely-used applications such as Microsoft Word and Adobe Acrobat Reader. For example, domains like “2024.xlsx.zip” and “fact03240175.pdf.zip” appear to be regular document files but are actually compressed files. This tactic is designed for tricking users into believing they are opening legitimate documents, increasing the risk of inadvertently downloading malicious files and executing malware.
As mentioned earlier in the blog, if a user searches for an .xlsx file that doesn’t exist, Windows will automatically open the web browser, putting the user at high risk of unintentionally downloading a malicious file. Similarly, if such a filename is mentioned by error in Slack or other chat apps, it can be automatically hyperlinked, leading to potential accidental downloads.
This is exactly what we observed in the data analyzed in our research. The domains that matched in our traffic are most probably ones that real users were unintentionally trying to download. Examples include “2024.xlsx.zip”, “courrierdevotrecaisse.pdf.zip”, “moteurs.docx.zip”, and “msoffice365update.zip”.
Domains that include installers are the most interesting because they have the potential to install malware directly onto users’ systems. These domains are particularly dangerous as they impersonate widely-used software and trusted brands, making them highly effective at deceiving users. Our deeper examination reveals that Microsoft-related domains dominate, accounting for 47.22% of the total malicious installer domains. This is followed by Google at 8.33%, with other brands like Apple, Adobe, Zoom, and Firefox each having smaller yet significant shares. The prevalence of these brands underscores a strategic effort by cybercriminals to exploit user trust and the urgency to update software. These insights highlight the dangerous nature of the .zip domains, revealing how they can be leveraged to spread malware and deceive users on a large scale.

Further analysis of the malicious installer domain names reveals a strategic use of specific keywords to deceive users and distribute malware. “Update” appears in 56 domains, exploiting the urgency to keep software current. “Installer” is found in 38 domains, often disguised as legitimate software installers. Security-related keywords are in 8 domains, leveraging fears of vulnerabilities. Additionally, “setup” appears in 10 domains, commonly used in initial configurations. These insights underscore the dangerous nature of .zip domains and the critical need for vigilance and robust cybersecurity measures.
Lessons Learned and Future Outlook
The Google .zip TLD underscores cybersecurity challenges related to domain name confusion, a problem Google emphasizes is not new. They stress the need for continuous monitoring and proactive measures to address these risks. Looking ahead, Google advocates for adaptive security strategies and comprehensive user education to enhance online safety. Despite these efforts, the .zip TLD remains a tool that can be exploited by attackers, necessitating continuous vigilance and proactive DNS security measures.
EfficientIP’s Protective DNS Security Solution plays a crucial role in mitigating these risks. By leveraging advanced AI-driven threat detection and DNS-centric threat intelligence, EfficientIP offers robust protection, real-time threat detection, and automated response and recovery capabilities.
EfficientIP’s advanced capabilities include patented DNS traffic inspection and behavioral analysis, which allow for precise identification of suspicious activities and potential sophisticated threats such as phishing, malware, spyware, data exfiltration through zero-day malicious domains, DNS tunneling, command and control…. Micro-segmentation with fine-grained, centrally managed DNS traffic filtering policies using Client Query Filtering (CQF) enhances zero trust security by ensuring only authorized users can access specific resources, enabling dynamic domain filtering based on the user’s group and permissions. Adaptive countermeasures and rescue mode provide swift, automated responses to mitigate the impact of attacks and maintain service continuity. Advanced AI-powered algorithms, such as Tuple Clustering, natural language processing, and image recognition , enable proactive identification of sophisticated DGA and phishing threats. Together, these features help reduce the risk of attackers misleading users and exploiting domain names like .zip, ensuring a higher level of network security.
This comprehensive approach is essential for maintaining network security in the face of evolving threats.
Conclusion
One year after the launch of the Google .zip TLD, it is clear that while it has potential for legitimate use, it also introduces significant security risks. Continuous vigilance and protective actions by both domain registrants and users are essential to mitigate these risks. Enhanced cooperation among registry operators, cybersecurity experts, and users is crucial for developing robust measures against DNS-based threats.
Stay informed about developments in TLD cybersecurity and DNS security. EfficientIP’s DNS Security solution offers a robust defense against emerging threats. For a practical demonstration of DNS Security, click here.