Consensus forms on reauthorizing 2015 cyber info-sharing law now,...
Year: 2025
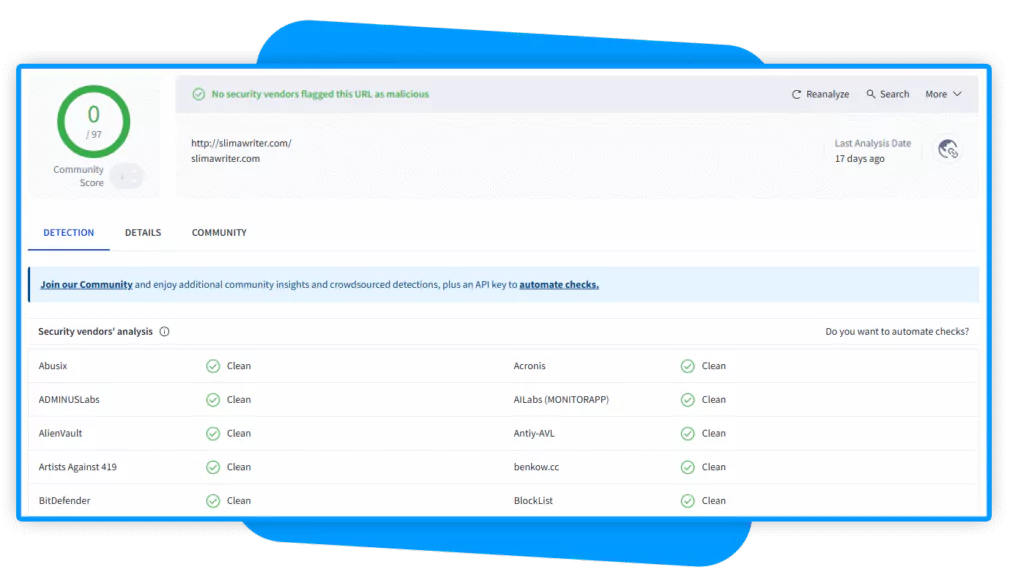
EfficientIP DNS Threat Intelligence Stops Zero-Day Malware Skip to...
Preparing for the post-quantum era: a CIO’s guide to...
FTC wants a new, segregated software system to police...
Proofpoint to acquire Hornetsecurity for over $1 billion |...
FBI warns of fake texts, deepfake calls impersonating senior...
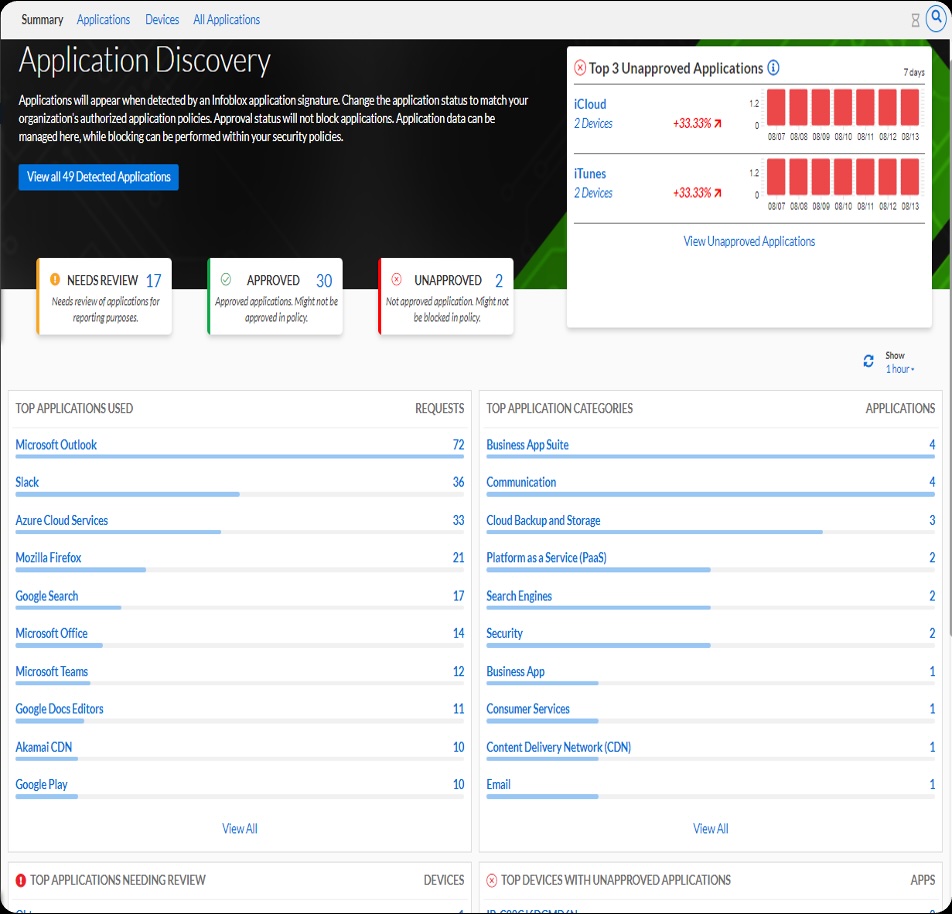
Generative AI applications have exploded in usage by organizations...
SAP cyberattack widens, drawing Salt Typhoon and Volt Typhoon...
North Korea’s ‘state-run syndicate’ looks at cyber operations as...
Who needs VC funding? How cybercriminals spread their ill-gotten gains to everyday business ventures
Who needs VC funding? How cybercriminals spread their ill-gotten...