The NIS 2 directive underscores the importance of robust...
compliance
Disclaimer: This blog offers general information and should not...
ThreatSTOP and FiveBy provide a unique combination of sanctions...
Automating OFAC compliance through ThreatSTOP can be as simple...
OFAC regulations restrict businesses and individuals from conducting any...
North Korean cybercrime has been on the rise in...
Emerging regulations, like the revised U.S. FTC Safeguards Rule,...
Are you writing loans at your car dealership, printing...
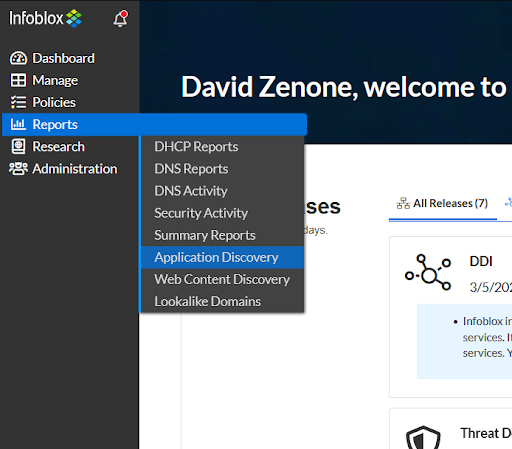
Network security teams know that getting visibility into the...