Executive Summary Halloween might be the spookiest time of...
Threat Intelligence
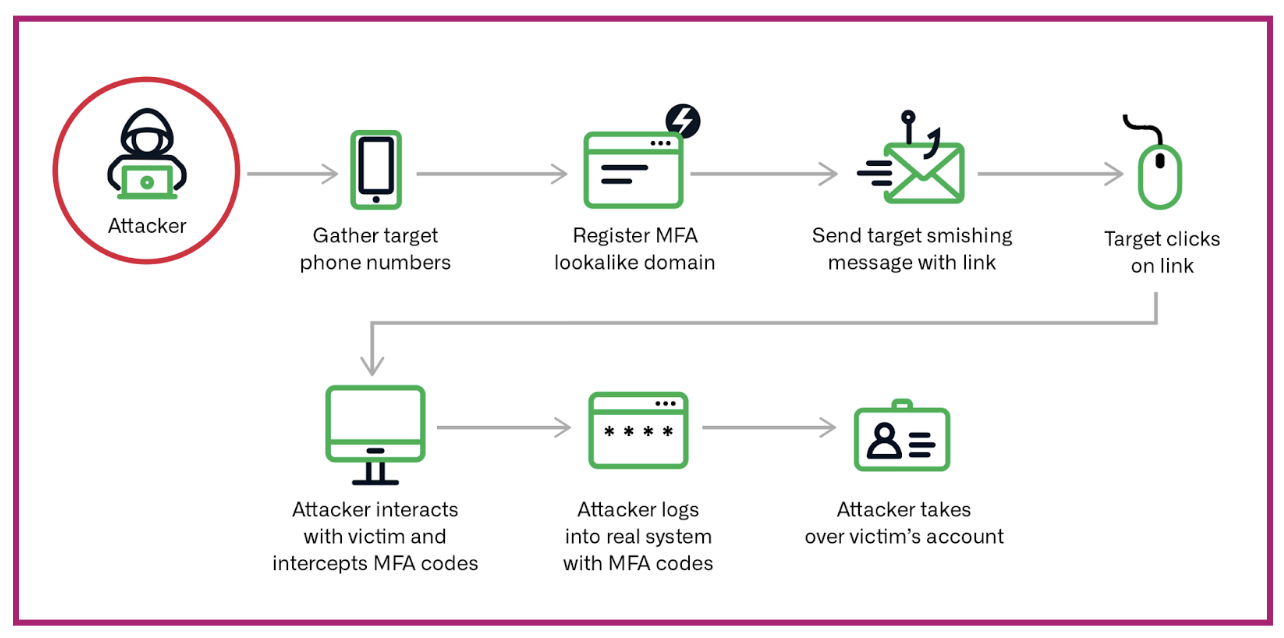
Over the last several years, the adoption of multi-factor...
With IT staff struggling to protect legacy networks on...
Author: Darby Wise Following our publication introducing the concept...
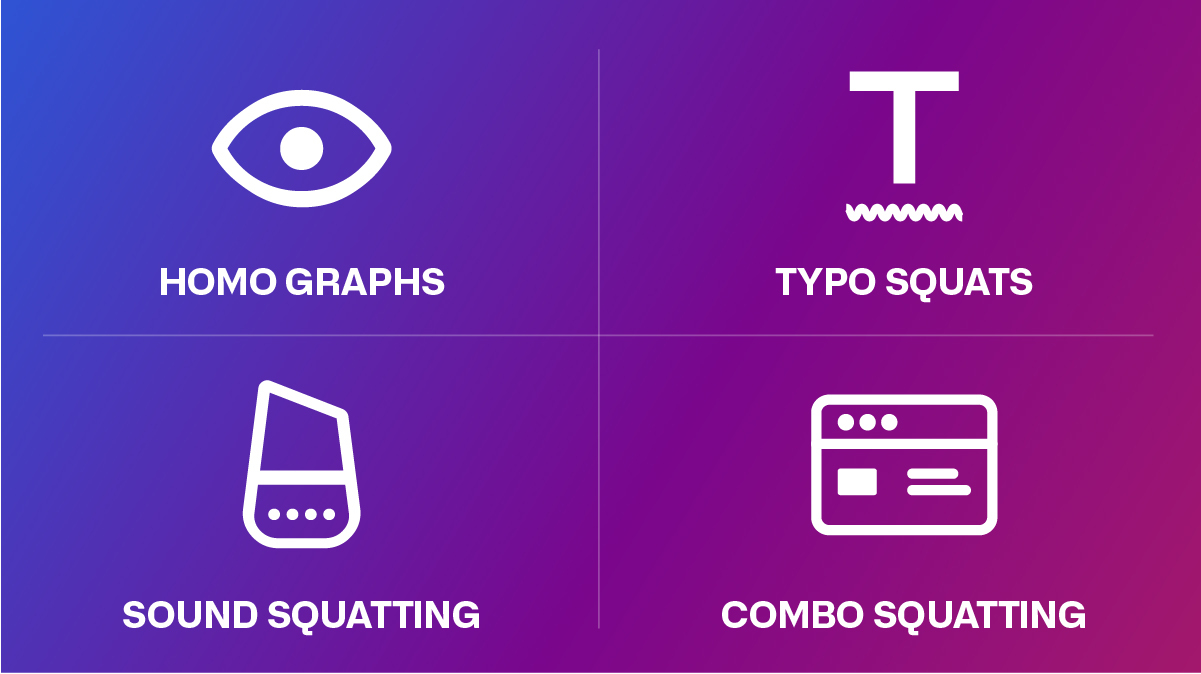
If you think you’re seeing double, you probably are....
Everyone loves a good whodunit. As the story of...
Year after year, the impacts and costs of DNS...
Introduction In today’s digital landscape, cybersecurity is of paramount...
Everyone wants to block threats before they are actively...
The Automated Indicator Sharing (AIS) by the Cybersecurity and...