Researchers at Microsoft have identified a North Korean threat...
Uncategorized
A political consultant identified as the individual who paid...
A proof-of-concept exploit (PoC) for a critical vulnerability in...
The BlackSuit ransomware gang has leaked stolen data from...
COMMENTARY Two decades ago, the economist Steven Levitt and...
A Pakistan-linked cyber-espionage group has pivoted to a wider...
Researchers have spotted a recent surge in activity involving...
In litigation, specificity is crucial. “Beyond a reasonable doubt”...
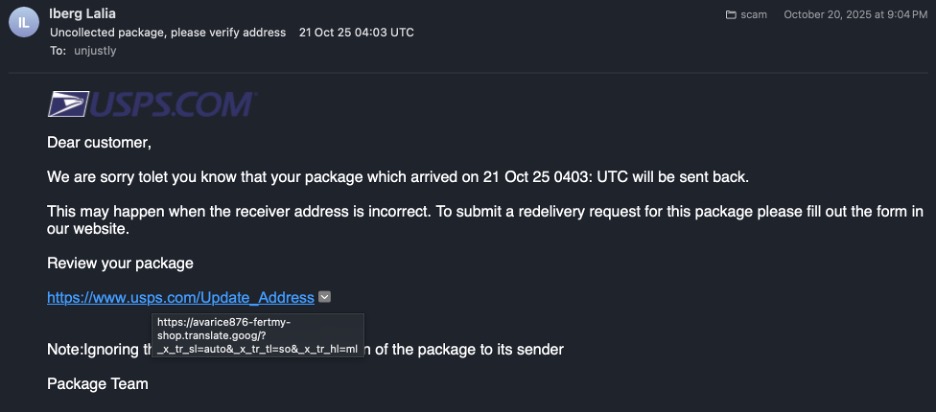
In recent months, researchers have observed an increase in...
Open AI is forming a safety and security committee...