Europe is trading security for digital sovereignty | CyberScoop...
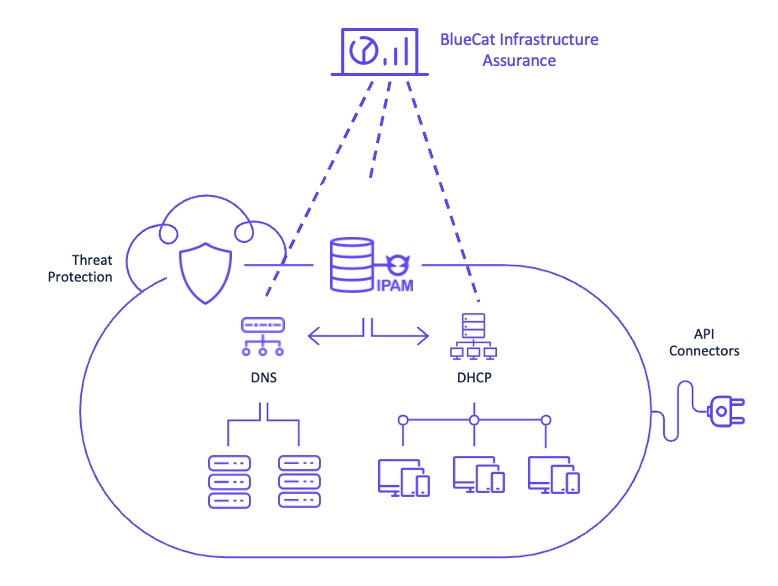
From disabled backups to configuration drifts, many types of...
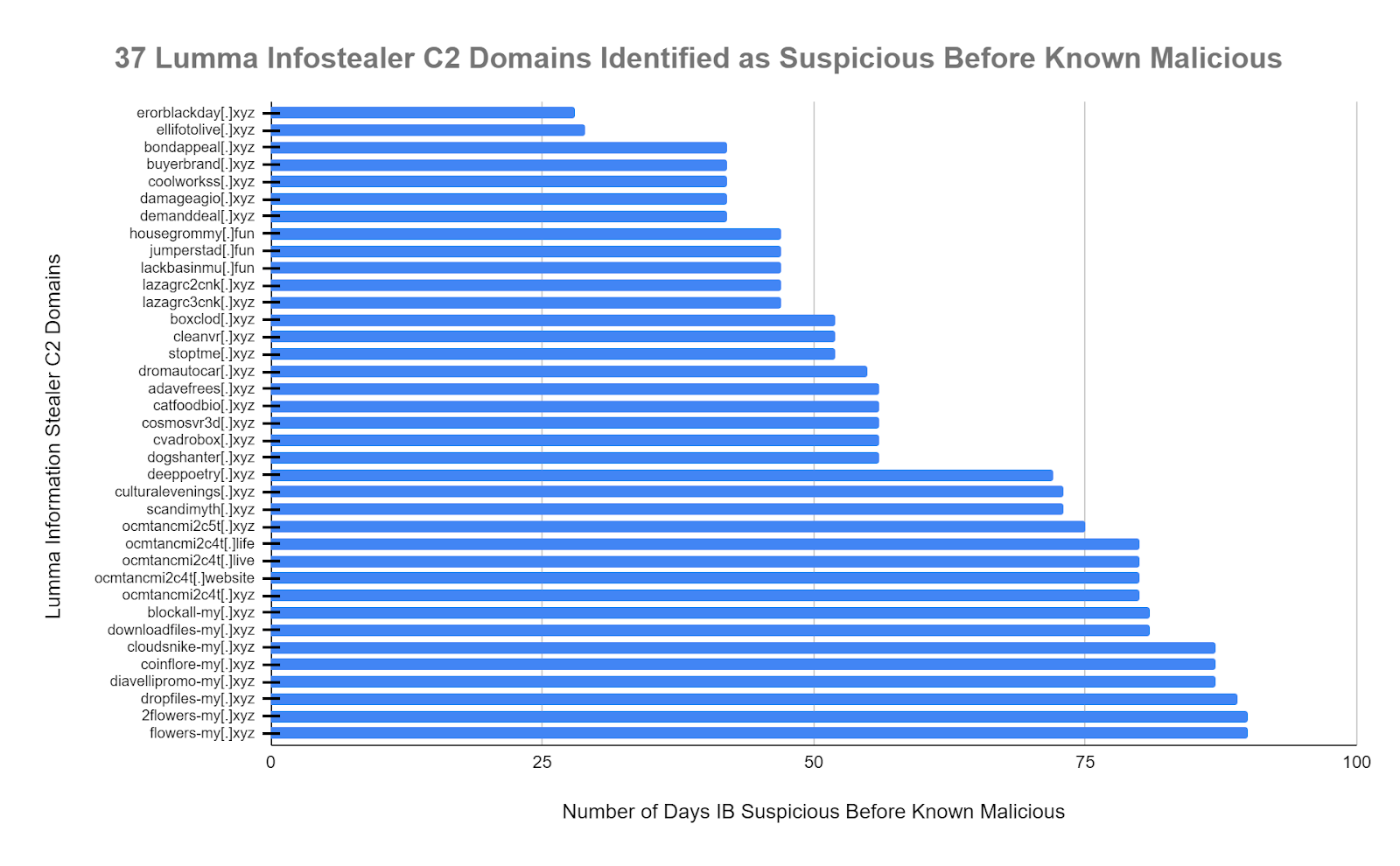
DNS for Early Threat Detection – Lumma C2 Only...
In an increasingly Internet-connected world, application programming interfaces (APIs),...
If you’re not already using crisis simulations as a...
Proof of concept (PoC) exploit code for a critical...
Ace Hardware has yet to recover many of its...
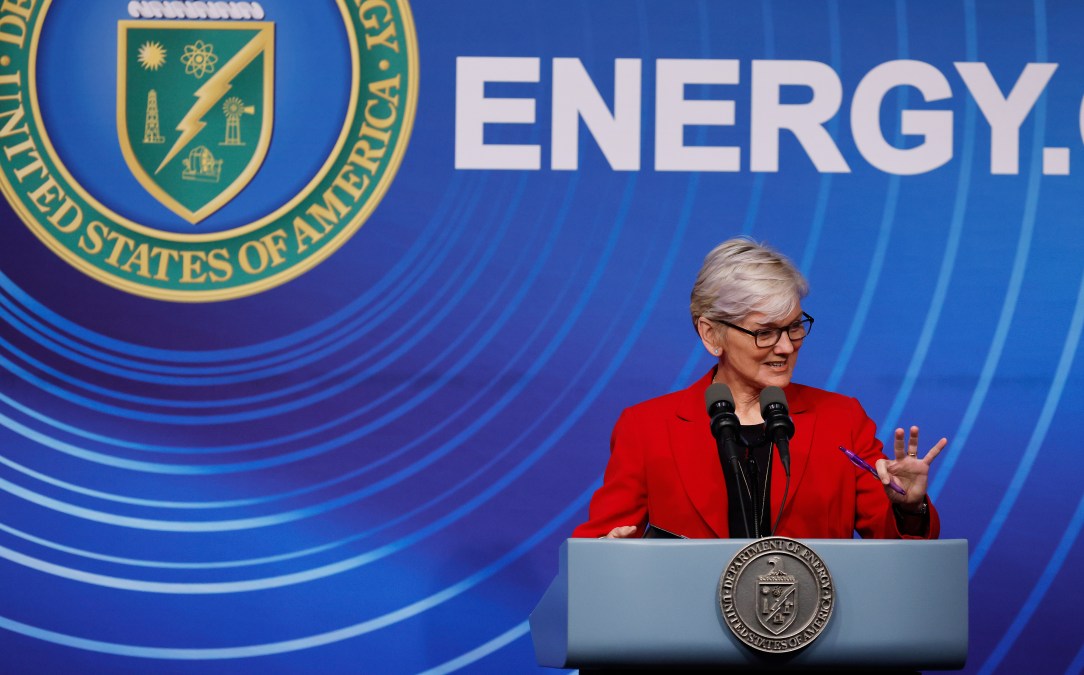
DOE hosting simulated cyberattack for students | CyberScoop Skip...
Okta has confirmed that threat actors were able to...
The infamous North Korean advanced persistent threat (APT) group...