This is the second in a three-part, in-depth report...
TDS
“Everyone knows that eliminating spam is impossible to achieve,...
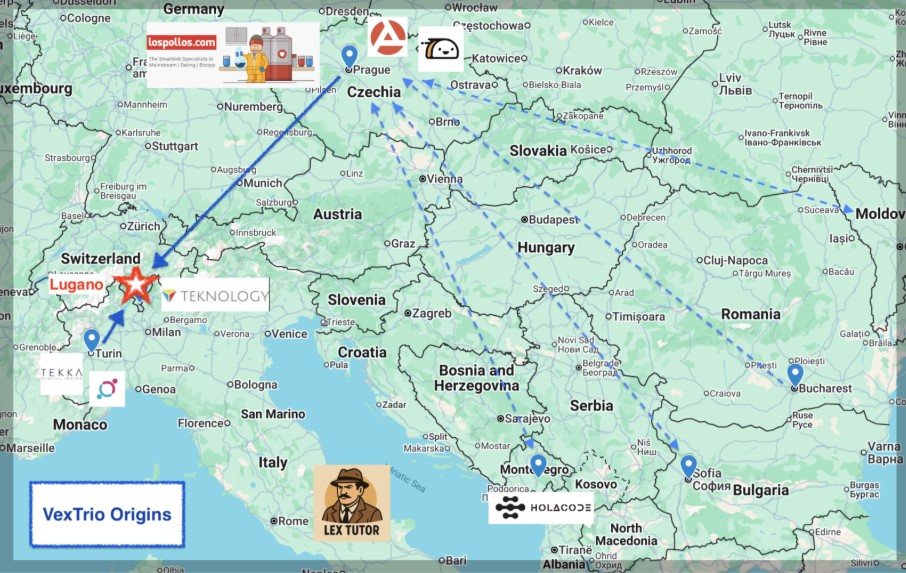
Executive Summary What started out as an observational study—perturb...
A recent cybersecurity advisory1 from the Cybersecurity and Infrastructure...
The stereotypical picture of a hooded figure hacking from...
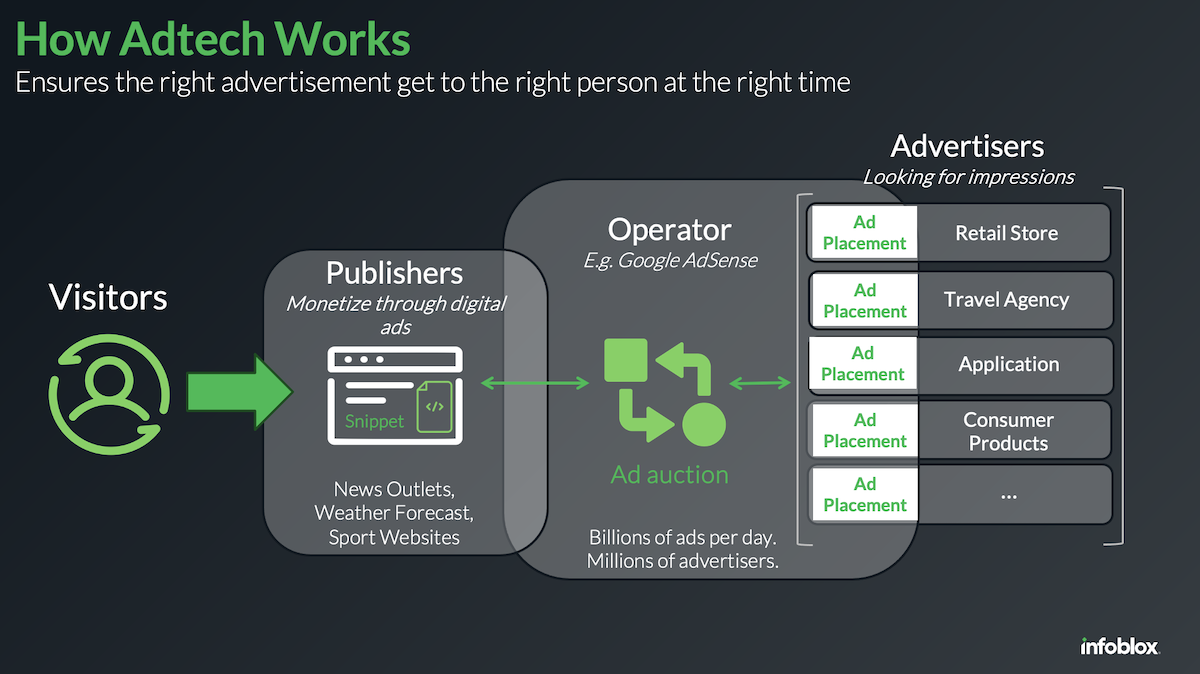
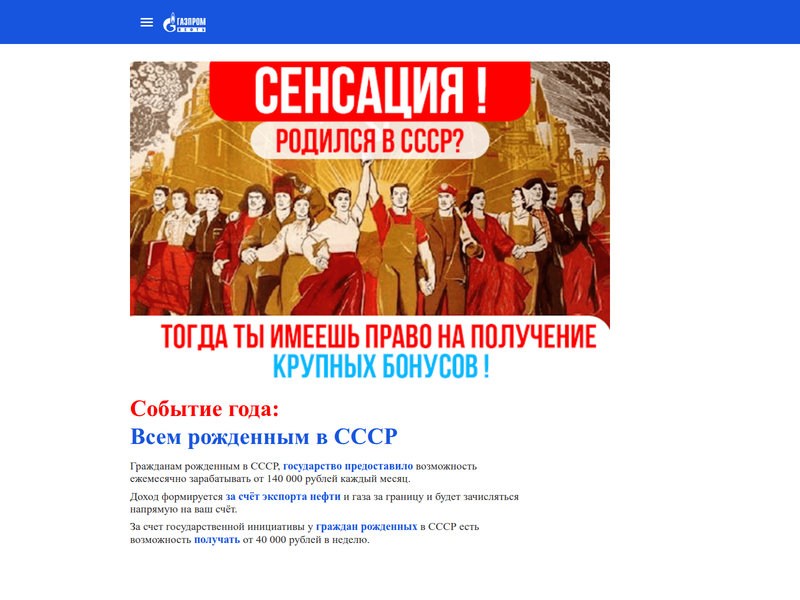
The Dangerous Combination of Compromised Websites and Malicious AdTech...
Authors: Bart Lenaerts and Tom Grimes Expert observations from...
Hijacking domains using a ‘Sitting Ducks attack’ remains an...
DNS provides a premier cybercrime route According to CISA,...
Malicious traffic distribution systems (TDSs) have flown under the...