“Good enough” security checks the boxes and keeps the dashboards green. It covers the basics and gets you through onboarding. But in MSP environments, “good enough” usually means nothing breaks badly enough to force action. And that’s exactly the problem.
The tooling system doesn’t fail. It just becomes more expensive to run, gradually turning your service desk into a permanent cleanup crew.
Over time, reactive security tools create a profitability problem that many MSPs don’t fully recognize until margins are already under pressure: rising ticket volume, technician time lost to repetitive work, and client risk that eventually becomes your business risk.
At small scale, it’s manageable. Across hundreds or thousands of endpoints, it becomes the default workload. The real issue isn’t major incidents; it’s the flood of low-level alerts and dead-end checks that drain hours and burn out your team.
This is where the problem shifts from technical to operational. In managed services, security sets the workload. The more noise, the more hours your team spends just keeping clients steady.
And that directly affects margin.
The real cost is in the workload, not the license
MSPs tend to focus on license costs, but the real expense is the workload a tool creates once it’s deployed.
Every alert that turns into a ticket burns technician time that should go elsewhere. Over time, this drags down the whole service team. This is where “good enough” quietly breaks your economics.
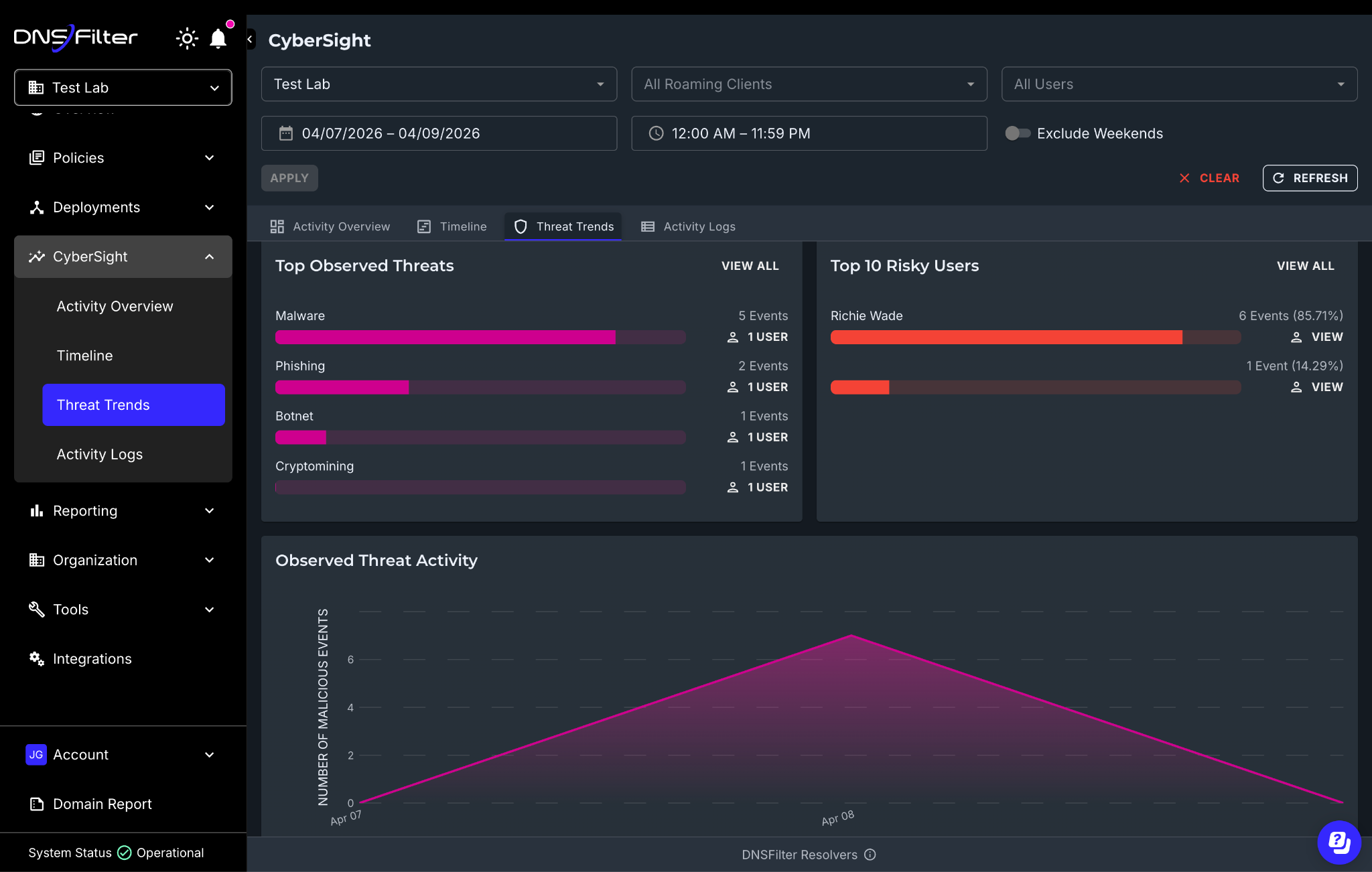
Here’s a simple way to look at it: If a reactive tool generates 5 extra security tickets per client per month and your average handling time is 20 minutes (triage, investigation, notes, client update), that’s 100 minutes per client per month (~1.7 hours)
Across 100 clients, that’s ~167 technician hours/month. Roughly one full-time tech spent on preventable noise.
Even if your numbers are different, the pattern holds: Small inefficiencies add up fast.
To absorb that load, headcount increases. Additional tools are introduced for coverage or visibility. The stack expands, but the volume of work doesn’t decrease.
Operational inefficiency, not tool failure, is what quietly kills profitability.
False positives create two problems that hit MSPs hardest.
First, they drive up operational overhead. Every alert needs checking, harmless or not. In multi-tenant MSP life, “quick checks” are never quick, because your techs have to:
- Reload context for the client environment
- Correlate what the alert means in that tenant
- Document the decision to close it out
- Explain it to the client
Second, false positives degrade signal quality. Too many dead-end alerts and your team loses focus. The line between routine and real threat blurs, and response quality drops.
Worse, false positives train clients to doubt your whole program. If your reporting and alerts feel unreliable, clients don’t think, “Our tool is too sensitive.”
They think, “Are we actually covered?”
Risk still sits in the background
Reactive tools don’t remove risk. They just respond after the fact.
The sequence is always the same: a user clicks, a domain resolves, and a connection is made. The system only reacts once the process is already moving.
Sometimes the threat is contained. Sometimes it isn’t.
For MSPs, a single incident rarely stays isolated. It spreads across endpoints, triggers escalations, and eats up after-hours time. Even if you clean it up fast, the business impact is real: Clients get nervous, stakeholders ask what was missed, trust takes a hit, and renewal conversations get harder.
Over time, that risk extends beyond the technical environment and into retention and reputation. This leaves MSPs carrying both the operational cost of response and the residual risk that reactive models can’t fully eliminate.
Reducing the amount of work changes the equation
The answer isn’t processing alerts faster. It’s cutting unnecessary alerts at the source to reduce workload and cost.
Every connection starts with a DNS request. If that request never resolves, the rest of the chain doesn’t happen. If there’s no connection, there’s no alert, no ticket. Block risky domains at the DNS layer, and you remove a whole category of downstream work. Your team never has to manage it after the fact.
For MSPs, that translates to:
- Fewer tickets
- Fewer escalations
- Fewer late-night “is this real?” investigations
- More predictable workload across the service team
Where your margin is actually decided
Security is typically framed as risk management. In MSP environments, it also determines how efficiently the business operates.
If your security model creates more work, you pay for it with more people, more tools, or both.
If the model removes work, the cost to support each client stabilizes. Your team has more capacity for higher-value activity, and growth no longer depends on proportional increases in headcount. You’ll see it in the numbers: Lower ticket volume, faster resolution times, better technician utilization, and stronger margins.
“Good enough” security doesn’t fail outright. It just makes scaling your business more expensive than it should be.
Try DNSFilter for yourself with a free trial. See how DNS-layer protection stops threats earlier, reduces tickets, and helps your MSP scale without adding headcount.